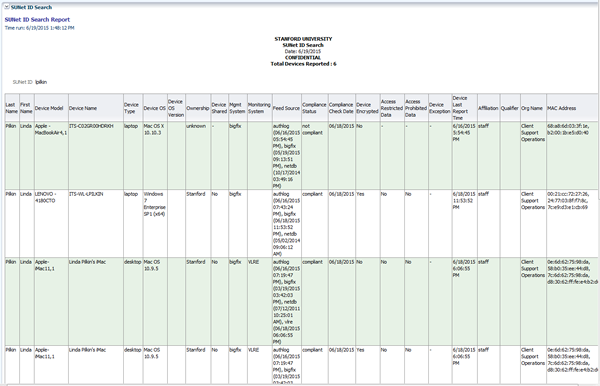
SUNet ID Search Report
The SUNet ID Search report returns all the devices (desktop and laptop computers, mobile phones, tablets, etc.) that are associated with an individual.
Procedures
- Enter either a single SUNet ID or multiple SUNet IDs, separated by a semicolon. Once the SUNet ID is entered, click anywhere in the header to make the Apply button active.
- The report can be sorted by any column. To sort the report, hover over the column heading and click either the up or down arrow.
- The report can be exported to PDF, Excel, PowerPoint, or a data file. Click the Export link on the bottom of the report to export the data.
- You may notice that some information is missing or not correct. Please have your IT support person check the applicable source system to ensure that the data is present and/or correct.
Column definitions
| Column Name | Description |
|---|---|
| SUNet ID | SUNet ID of device owner. |
| Last Name | Last name of SUNet ID. |
| First Name | First name of SUNet ID. |
| Device ID | ID assigned by the device registry to the device. |
| Device Model | Model of the device reported by the source system. |
| Device Name | Name of device as entered by device owner or reported by the source system. |
| NetDB Node Name | Name of the device in NetDB. |
| Device Type | The type of device as reported by the source system. |
| Device OS | The OS major/minor version as reported by the source system. |
| Device OS Version | The OS version as reported by the source system. |
| Ownership | Whether the device is owned by Stanford or is a personal device, as reported by the device owner. |
| Device Shared | Whether the device is shared, as reported by the device owner. |
| Mgmt System | The system, either MDM or BigFix, which manages the device. Mobile devices are managed by MDM, and laptops and desktops are managed by BigFix. |
| Monitoring System | The system that monitors the device. Laptops and desktops are monitored by VLRE. |
| Feed Source | The system(s) that supplied the data for the report. |
| Compliance Status | Whether the device complies with the University's security mandate. |
| Enforcement Status | Whether University's security mandate is enforced or not enforced for this device. |
| Device Encrypted | Whether the device has been encrypted, as reported by its management system. |
| Non-Compliance All Reasons | Reasons the device is listed as non-compliant. |
| Non-Enforcement All Reasons | Reasons the security mandate is not enforced on this device. |
| Access Restricted Data | Whether the device owner can access Restricted Data, as reported by the device owner. |
| Access Prohibited Data | Whether the device owner can access Prohibited Data, as reported by the device owner. |
| Device Exception | Whether the device has an exception to the encryption requirement, as reported by the Exception Request system. |
| Device Last Report Time | The last time the device was seen on the network. |
| Disavowal Date | Date that the device was disavowed. |
| Disavowal All Reasons | Reason the device was disavowed. |
| MAC Address | The MAC address(es) as reported by the source system. |
Management system = BigFix or MDM
Source system = the source system for the data (may be NetDB, BigFix, MDM, Exception Request system, Authorization Logs)
Last modified
