Data Risk Assessment
Getting started with DRAs
As the volume of Stanford data continues to grow exponentially, so do the risks associated with storage, processing, and management. To safeguard sensitive information, the University Privacy Office (UPO) and Information Security Office (ISO) conduct data risk assessments (DRAs).
A DRA is a review of whether a proposed transfer Moderate or High Risk data to a non-Stanford entity is consistent with Stanford’s Minimum Security Standards and Minimum Privacy Standards. Before sending or receiving Moderate or High Risk data to or from a non-Stanford partner, you must submit a DRA to evaluate the extent of risk to the university. OneTrust is a tool to request, track, collaborate on, and automate DRAs at Stanford.
Who should submit DRAs and for what reasons?
- Stanford researchers and other teams should submit a DRA request before sending or receiving "Moderate Risk" or “High Risk” data (as defined under Stanford’s Risk Classifications) to or from a non-Stanford or external entity.
- If the non-Stanford or external entity sending or receiving the High Risk data has no direct relationship with Stanford but does have a contractual agreement with the sponsor or Clinical Research Organization (CRO) to provide the services — e.g., use of electronic data capture (EDC), electronic case report forms (CRFs), or electronic diaries — a DRA review of that non-Stanford partner is typically not required. The sponsor/CRO assumes the responsibilities for managing the privacy and security risks associated with that third party relationship.
- Non-Stanford or external entities that support Stanford hospitals, where the contract falls under the hospitals, should not go through this DRA process. Please reach out to the Hospital Privacy Office at PrivacyOfficer@stanfordhealthcare.org, or the Hospital Security Office on privacy or security questions.
What information will I need to provide when completing the DRA form?
In the revised automated DRA submission form, you’ll be asked questions related to Stanford’s Minimum Security Standards (minsec.stanford.edu) and Minimum Privacy Standards (minpriv.stanford.edu). If you have all of the necessary details, it will take less than 45 minutes to complete the form.
Please be prepared to provide the following details in responding to the questions:
- All the data element types to be sent or received by Stanford
- The purposes of the data use and transfer
- The project’s IRB protocol number
- The non-Stanford entities that will provide, process, or receive PHI/PII
- Copies of relevant Data Use Agreements (DUA)
- Copies of Waivers
- Copy of draft Notice and Consent document, if data will be collected directly from participants
- Confirmation that all project members have successfully completed HIPAA or other privacy training
- The project’s go-live date (past or future)
- Where the data will be stored within Stanford
- What the recommended retention period for the PHI/PII data is and how long your team anticipates project data will be kept.
- If working with a non-Stanford entity, the name and contact email of the entity, and whether they have previously provided services to Stanford.
- The non-Stanford entity will also have to respond to a separate non-Stanford entity questionnaire relating to their security practices, and provide copies of the non-Stanford third-party attestations.
Note: For China-based studies, please reach out to the Privacy Office at https://privacyrequest.stanford.edu for a consultation before submitting a DRA.
About OneTrust
OneTrust optimizes Stanford’s DRA system, process, and user experience with many key features, including:
- A simplified, smart DRA submission form
- Reduced processing time and administrative burden
- Robust notifications and alerts
- Instantaneously generated reports
- Minimum security and privacy requirement guidance specific to your data use
As you use OneTrust to walk through the DRA form and process, we invite you to share about your experience to help us continually improve the system.
What's the DRA process?

*If working with a vendor, the system will notify the vendor to complete a separate assessment. External or non-Stanford entities that are not vendors should have a data use agreement (DUA) with the university and are not sent a separate assessment in OneTrust.
For the majority of DRA submissions, the automated report is generated immediately after submitting the assessment. Please note that the Notice of Completion after completing the DRA review is not an approval of your project. You will still need to secure approval from the Institutional Review Board (IRB), or any other body that is authorized to approve your project.
Follow the Risk Mitigation instructions to complete steps 3 and 4 in the process.
FAQ: Using OneTrust
Get to know the OneTrust interface
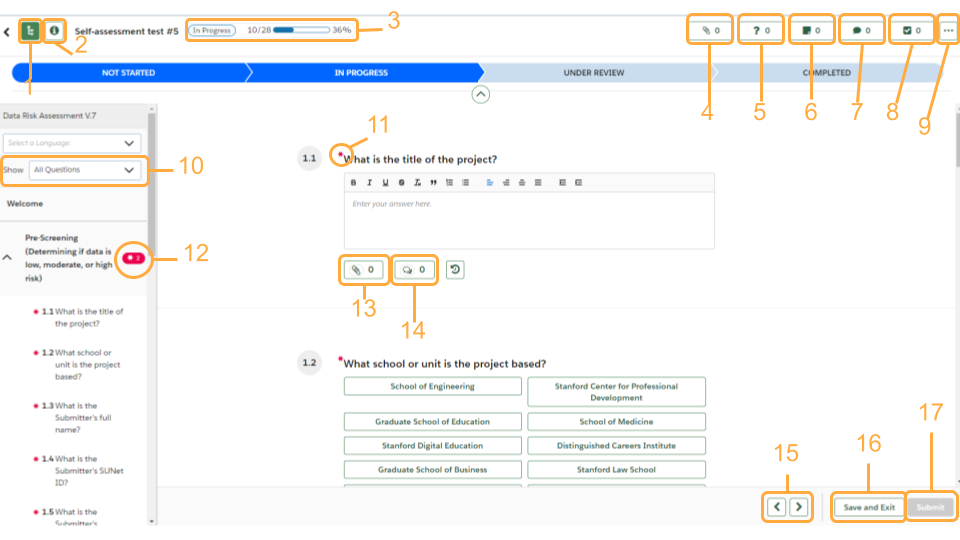
- Controls the left panel of sections
- View the details of your assessment
- Progress tracker
- See what attachments have been uploaded
- Knowledge requests: if a reviewer needs more information regarding an answer the requests will be listed here
- Notes: if a reviewer has left any notes they will be listed here
- Any comments left for questions will be listed here
- Any tasks associated with the DRA will be listed here. An example would be a task for risk mitigation
- More options: Downloading your assessment
- Filter what questions you see listed
- “*” denote required questions
- If there are required questions left unanswered in a section there will be a red bubble with the “*” symbol and how many required questions still need responses. You can click this bubble and be navigated to the first unanswered required question
- Click to attach a file
- Click to leave a comment for a question
- Navigate between sections
- Save and Exit button: Use this if you need to pause and come back to your DRA
- Submit button: bright green when you have answered all the required questions; grayed out when form is incomplete
How do I submit a new DRA request in OneTrust?
- Log into OneTrust with your SUNet ID and password.
- Select either "DRA with IRB" or "DRA without IRB" based on your project type.
- Click the green Launch Assessment button.
- Enter a name for the assessment.
- Click the green Launch button at the bottom right of screen.
- Navigate to the “Pre-screening” tab in the left panel to begin the form.
- Complete the required questions marked with an * within each section.
- Click Submit at the bottom right of screen.
After submitting:
- You will receive a confirmation email only if your submission is auto-approved, meaning no high risks were identified;
- Or you will also receive individual emails assigning you as a risk reviewer, prompting you to attest to and mitigate risks associated with your project.
TIPS:
- To advance to the next section at any time, click the > at the bottom of the interface.
- The sections you are required to fill out are seen on the left-side panel and required questions are marked with asterisks. If a section is not required for your DRA case, it will be grayed out.
- The assessment will auto-save your answers each time you proceed to a new question. You can also save and exit the assessment at any time by clicking “Save and Exit” at the bottom right of your screen. You can come back to your assessment as needed until it is submitted.
How do I submit additional documentation once I've already submitted?
Some questions will require documentation before submitting the form. However, if you have additional documentation to add after submitting the form or to view current attachments, follow these steps:
- Log into OneTrust with your SUNet ID and password.
- Click the notification icon in the top menu bar and find your most recent assessment.
- Open that assessment and navigate to the question number that requires an attachment.
- Click the attachment button to upload a file.
How do I add other members of my team as respondents on the form?
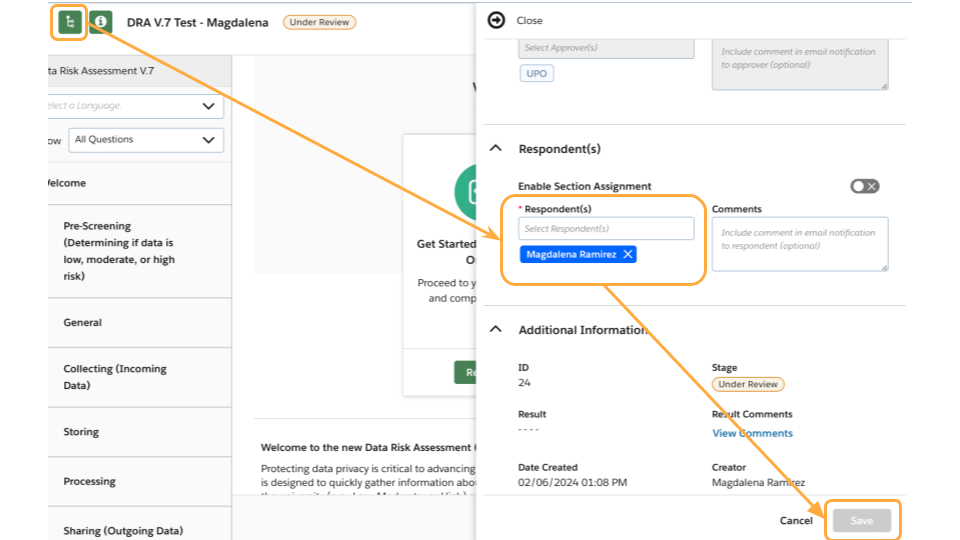
- Within your assessment, click the green information button on the top left.
- Click the arrow next to Respondent(s) to expand the section.
- Enter any additional respondent to the form and optional comments.
- The Respondent(s) will receive an email from the system with an invitation to open and respond to the assessment.
How does the tool involve vendors or non-Stanford entities?
After the requester completes their assessment, the vendor is notified to complete a separate assessment in OneTrust. Non-Stanford entities that are not vendors should have a data use agreement (DUA) with the university and are not sent a separate assessment in OneTrust.
How do I view my flagged risks and treatment plans?
- After submitting the DRA, you will be notified by the system to view the flagged risks.
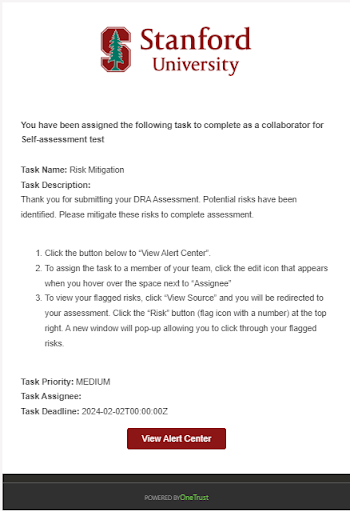
- When notified, click the View Alert Center button within the email to open the Risk Mitigation page in OneTrust.
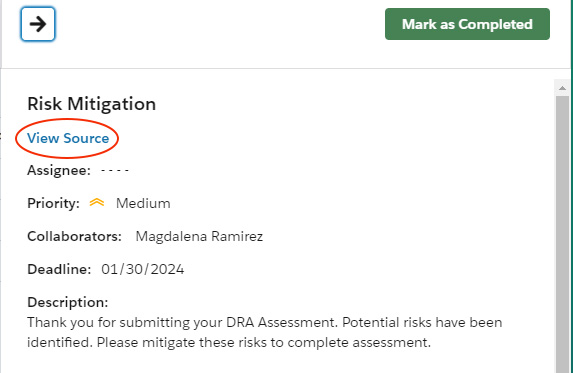
- Click the flag icon in the top navigation to open the list of flagged risks.
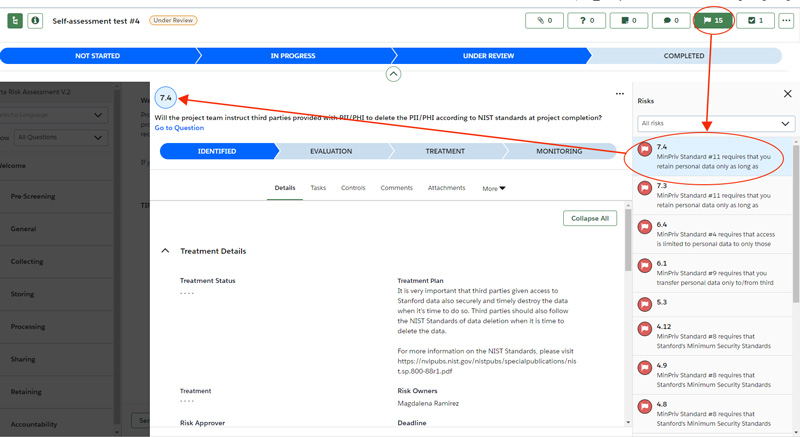
- Review the risks and the recommended treatment plans to mitigate risks for each risk. The number next to the flag corresponds with the question number.
- Follow the Risk Mitigation instructions under "Risk treatment plans" for step-by-step guidance on completing the process in OneTrust.
- After submitting the DRA, you will be notified by the system to view the flagged risks.
What steps should I take after completing the recommended mitigation steps in my treatment plan?
Follow the Risk Mitigation instructions for step-by-step guidance on completing the process in OneTrust.
I'm having trouble accessing content on OneTrust due to a disability. What should I do?
The Stanford DRA team is actively working with OneTrust to remediate accessibility issues within OneTrust. In the meantime, we ask that you reach out to us at dra_review@lists.stanford.edu for guidance on submitting through the legacy DRA system.
Additional help
DRA support
- DRA office hours: every Wednesday, 11 a.m. to 12 p.m. PT (except for holidays)
- For questions about the DRA process, please contact us at dra_review@lists.stanford.edu
