Goodbye WebAuth, Hello SAML
Whether reading email, accessing online files, processing financial transactions, or countless other activities that help us do our jobs and keep Stanford running, most of us spend a good portion of our days online.
And as we connect to the host of online resources that help facilitate our work, we often have to enter our Stanford account and password. That’s when the magic happens. Well, it’s really not magic. For years, a homegrown system called WebAuth has protected the university’s online assets while enabling community members and trusted colleagues around the world to access any number of systems with just one login action. That system is changing.
Over time, University IT will be transitioning away from WebAuth to power the authentication and authorization systems to a new, more widely adopted standard.
What is Stanford changing to and why?
As familiar and trusted as WebAuth may be, it is homegrown and not used by many of the third-party service providers whose services must be integrated with Stanford’s computing environment. Unlike when WebAuth was initially developed, today Stanford can both leverage and contribute to the innovation and ongoing development of more broadly used standard solutions. We no longer need to invest in maintaining and enhancing a unique application.
That’s why the university is now moving to Security Assertion Markup Language (SAML), a widely-adopted, consolidated single sign-on standard already in use here for years, that will work with all of the services and organizations the Stanford community connects with on campus and around the world.
How will this affect me?
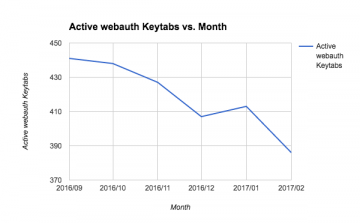 Recent system metrics show a decline in active WebAuth "keytabs" (a keytab is file containing Kerberos keys) since last September, indicating that server and application owners are on board with the transition to the new single sign-on method.
Recent system metrics show a decline in active WebAuth "keytabs" (a keytab is file containing Kerberos keys) since last September, indicating that server and application owners are on board with the transition to the new single sign-on method.
For everyday users of protected websites and apps, the transition from WebAuth to SAML won’t require attention or action at all. There may be small changes to the look and feel of WebLogin and other screens where people enter their SUNet ID password, but everything — including two-step authentication — will work just as simply, and as well.
The change mostly affects people who manage a server or application using WebAuth. The UIT team that registers and helps configure these systems has been setting up workflow processes and supporting early system migrations while others have been focusing on documentation, training, and outreach. All will continue their efforts over the months ahead.
Is this change surprising? Scary? It shouldn’t be, really. For over 12 years, UIT has used a SAML Identity Provider (IdP) for partner-provided services such as Office 365, Google Drive, Box, and the Qualtrics survey tool. Behind the scenes, some of us know these services as Shibboleth integrations (Shibboleth happens to be the most widely used implementation of SAML in higher education).
So you’re probably already using SAML — you just didn’t know it. And UIT has already been supporting it for many years under the Shibboleth name and service.
Where are we in the process, and what steps are ahead?
UIT has built the systems architecture enabling authentication of users directly via SAML, so we no longer need to rely on WebAuth. From here, targets for completion include the migration of half of the resources that UIT manages or provides by late spring 2017.
Learn more
For technical questions about WebAuth-to-SAML migrations, email shibboleth-partners@lists.stanford.edu.
For general questions about the Identity and Access Management (IAM) initiative, contact Bruce Vincent at bvincent@stanford.edu.
DISCLAIMER: UIT News is accurate on the publication date. We do not update information in past news items. We do make every effort to keep our service information pages up-to-date. Please search our service pages at uit.stanford.edu/search.